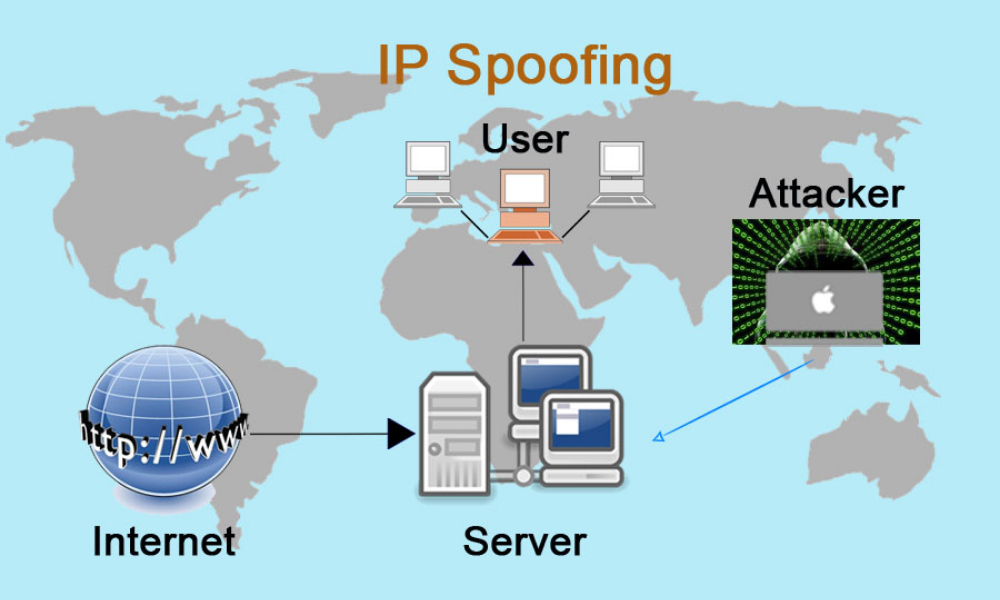
IP spoofing is the process of altering the source address of Internet Protocol (IP) packets to conceal the sender’s identity, mimic another computer system, or both. It is a technique that malicious actors frequently utilize to initiate DDoS assaults on a target device or the surrounding infrastructure.
IP packets are the principal means through which networked computers and other devices interact, and they form the backbone of the contemporary internet. All IP packets begin with a header that provides critical routing information, including the source address.
The source IP address of a typical packet is the address of the packet’s sender. The source address will be faked if the packet has been spoofed.
IP Spoofing is comparable to an attacker sending a package to the wrong recipient with the incorrect return address specified. If the recipient wishes to prevent the sender from sending packages, banning all packages sent to the phony address will be ineffective, as the return address is readily modified.
Additionally, if the recipient wishes to respond to the return address, their response package will be delivered to a location different than the original sender. The ability to fake packet addresses is a critical vulnerability that many DDoS assaults exploit.
DDoS attacks sometimes employ spoofing in order to overload a target with traffic while concealing the offending source’s identity, thwarting mitigation measures. When the originating IP address is fabricated and randomized constantly, preventing fraudulent requests becomes more challenging.
Furthermore, IP spoofing makes it more difficult for law enforcement and cyber security personnel to trace down the attacker.
Moreover, spoofing is used to masquerade as another device, causing replies to be transmitted to the targeted device. This vulnerability is exploited by massive assaults such as NTP amplifiers and DNS amplifiers. The capability to modify the originating IP address is built into TCP/IP, making it a persistent security risk.
Separate from DDoS assaults, spoofing can be used to impersonate another device to bypass authentication and get access to or “hijack” a user’s session.
How Spoofing Is Carried Out
The data carried over the internet is first divided into several packets, which are then individually transported and reassembled at the other end. Each packet comprises an IP header containing information about the packet, such as its source and destination IP addresses.
IP spoofing is a technique in which a hacker modifies the source address in a packet header to convince the receiving computer system that the packet is coming from a trustworthy source, such as another computer on a valid network, and so accepts it. Because this occurs at the network level, no outward evidence of meddling is visible.
This form of assault is frequently used in Denial-of-Service (DoS) attacks, which may cause computer networks to become overwhelmed with traffic. A DoS attack utilizes falsified IP addresses to flood Windows or macOS computer systems with data packets, thereby shutting them down.
Botnets – networks of infected computers — are frequently used to deliver messages. Each botnet may comprise tens of thousands of machines capable of faking a variety of different source IP addresses. As a result, tracing the automated assault is challenging.
A version of this strategy employs hundreds of machines to deliver messages to a large number of recipients using the same faked source IP address. Automatic acknowledgment is sent from the receiving computers to the faked IP address, flooding the targeted server.
Another technique of malicious IP spoofing employs a “Man-in-the-Middle” attack to disrupt connections between two computers, modify the packets, and then broadcast them without the sender or recipient being aware. Hackers amass a wealth of sensitive information that they may use or sell over time.
IP spoofing can be used to circumvent IP address authentication in systems that rely on trust connections between networked computers. The concept behind the “castle and moat” defense is straightforward: those who are not connected to the network are considered dangerous, while those who are connected to the castle are trusted.
Once a hacker has gained access to the network and is inside, it is rather simple to investigate the system. Given this weakness, basic authentication is being phased out in favor of more robust security measures, such as multi-step authentication.
Spoofing Techniques
The most prevalent types of spoofing are as follows:
- IP address spoofing — Masks the attacker’s origin IP address either it is static or dynamic. It is frequently used in denial-of-service attacks.
- ARP spoofing — Uses faked ARP packets to connect a perpetrator’s MAC address to a valid IP address. It is frequently used in distributed denial of service (DoS) and man-in-the-middle (MITM) attacks.
- Spoofing DNS servers – Modifies a DNS server to redirect a domain name to a different IP address. Typically, it is used to disseminate viruses.
Spoofing IP Address In Application Layer Attacks
To establish application layer connections, the host and visitor must engage in a procedure of mutual verification referred to as a TCP three-way handshake.
The procedure is as follows, packets of synchronization (SYN) and acknowledgment (ACK) are exchanged:
- A visitor initiates communication with a host by sending an SYN packet.
- The host acknowledges the request with an SYN-ACK.
- The visitor acknowledges receipt of the SYN-ACK packet by sending an ACK packet in response.
Spoofing the source IP address prevents the third step of this process from occurring since it prevents the visitor from ever getting the SYN-ACK response sent to the fake IP address.
Due to the fact that all application layer assaults rely on TCP connections and the completion of the three-way handshake loop, only network layer DDoS attacks are capable of using faked addresses.
Spoofing IP Address For DDoS Assaults
IP address spoofing is used in DDoS assaults for two reasons: to conceal the locations of botnet devices and to stage a reflected assault.
Botnet Device Concealment
A botnet is a collection of malware-infected devices that are controlled remotely by criminals without the owners’ knowledge. They may be directed to reach a certain domain or server collectively, giving offenders the computational and networking capabilities necessary to cause massive traffic floods.
Such floods enable botnet operators to exhaust the resource capacity of their targets, resulting in server outage and network overload. Botnets are often composed of randomly distributed devices or computers that are part of the same infiltrated network.
By masking the genuine identities of their botnet devices with faked IP addresses, offenders hope to do the following:
- Prevent law enforcement and forensic cyber-investigators from discovering and implication.
- Prevent targets from informing device owners about an attack in case they are unintentionally involved.
- Bypass security scripts, devices, and services that seek to mitigate DDoS assaults by IP address blacklisting.
DDoS Reflected Attack
A reflected DDoS attack takes advantage of IP spoofing to make seemingly legitimate requests on behalf of a target to elicit replies from unprotected intermediate servers. The attacker’s objective is to increase their traffic production by generating huge answers to many smaller queries.
Typical mirrored DDoS attack tactics include the following:
- NTP Amplification – A get monlist request is issued to an insecure NTP server with a target’s faked IP address. As with DNS amplification, a modest request results in a considerably bigger response, allowing for an amplification ratio of up to 1:200.
- Smurf Attack — An ICMP Echo request is issued from the faked address of the target to an intermediary broadcast network, eliciting responses from all devices on that network. The extent to which the request is amplified is determined by the number of devices to which it is broadcast. A network with 50 linked hosts, for example, results in a 1:50 amplification.
- DNS Amplification – Any query originating from the faked address of a target is transmitted to a large number of untrusted DNS resolvers. Each 60-byte request may generate a 4000-byte response, allowing attackers to increase traffic production by up to 170 times.
How To Prevent Spoofing
The majority of techniques for avoiding IP spoofing must be designed and applied by IT professionals. To guard against IP spoofing, organizations can monitor networks for unusual activity, implement packet filtering to detect inconsistencies such as outgoing packets with source IP addresses that do not match those on the organization’s network.
Employ robust verification methods even among networked computers, authenticate all IP addresses, and use a network attack blocker. Additionally, it is a good idea to isolate at least a fraction of computer resources behind a firewall.
Web designers are urged to convert their sites to IPv6, the most recent version of the Internet Protocol. By using encryption and authentication, it makes IP spoofing more difficult. The majority of internet traffic on the planet continues to utilize the previous protocol, IPv4.
As of mid-November 2017, the Seattle Internet Exchange, one of only two in the world that collects IPv6 traffic statistics, reports that only approximately 11% of traffic has switched to the newer, more secure protocol.
IP spoofing is practically impossible to detect by end-users. They may, however, mitigate the danger of other sorts of spoofing by utilizing secure encryption methods such as HTTPS — and only visiting websites that employ them as well.
Frequently Asked Question
Is IP spoofing a criminal act?
How do hacker spoof your IP ?
Is spoofing a crime on the internet?
Conclusion
Although this is not an exhaustive list of information on spoofing, since it is a big subject to cover, we have attempted to provide the finest content possible to dispel any doubts about the subject and educate our visitors about it by highlighting the critical parts of IP Spoofing.